
Ping’s output, by the TTL around 128, we know that is a Windows Machine

Ping’s output, by the TTL around 128, we know that is a Windows Machine


Nmap sCV scan, part 1

Nmap sCV scan, part 2
Nothing relevant

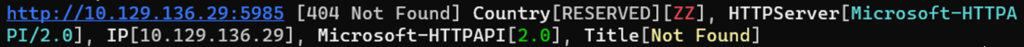
404 Again

A good sign for us.

Available Disk from the machine
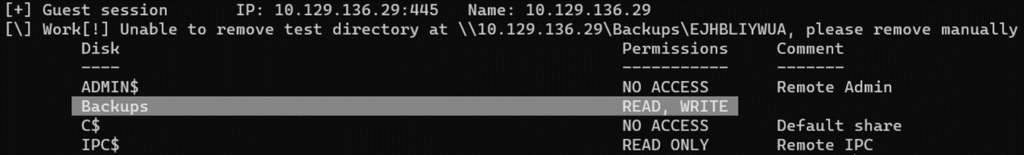
Disk Permissions


If you can access anytime through SMB, there is no hurry to download the target.
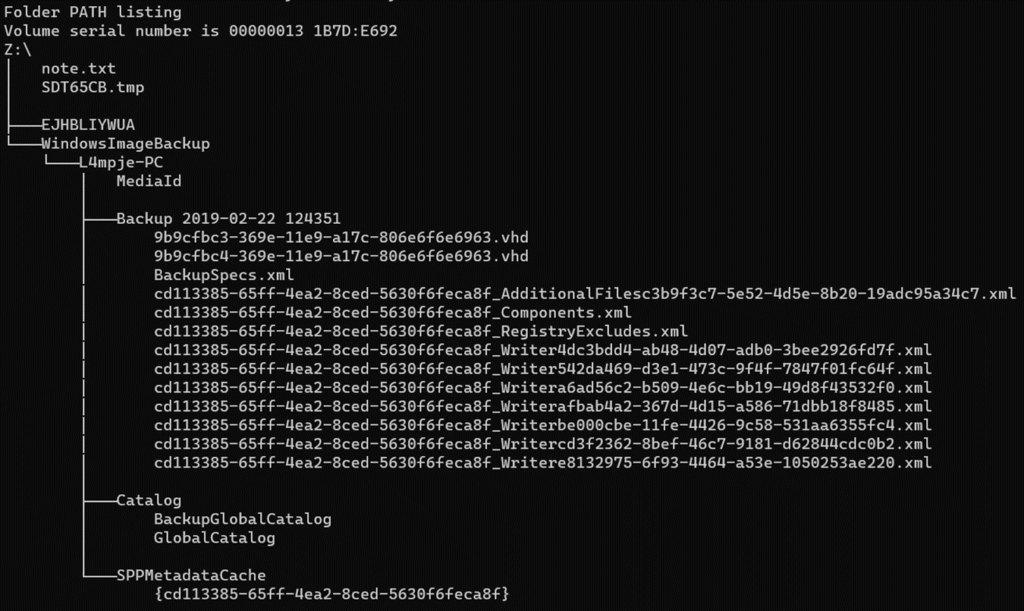
Entire content of Backup


Content of the location

output of impacket-secretsump

“data” file’s content

The hash is correct

Relevant Information: {L4mpje@bureaulampje}

Ok, definitely works. We can login with L4mpje and pass bureaulampje

IP config inside 10.129.136.29
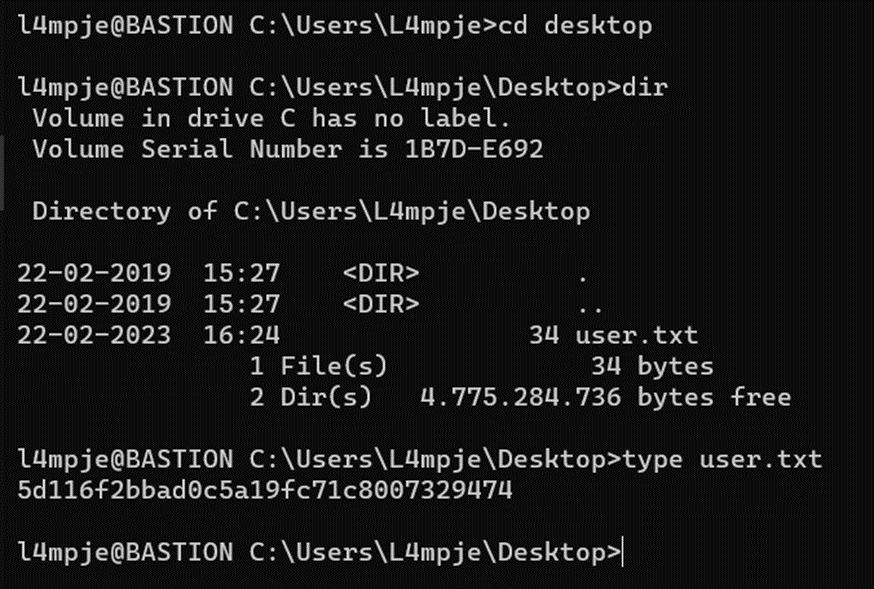
Previous steps, we have the first flag.

We are not Administrator

Both are not usual targets. Let’s check information about groups.

Commands output, nothing important

:(

:(

At this point, the best option is to navigate toward every folder.

Content of "Program Files"

Program Files (x86)



How to use

Administrator@thXLHM96BeKL0ER2




From here, you can do the same.