
Nmap’s output, just a website?

Nmap’s output, just a website?


Relevant information: Varnish 6.2, after exploring you should search about that.

Main page

Fragment of the main page source code (CTRL+U)

home, tickets, and reset. Interesting.


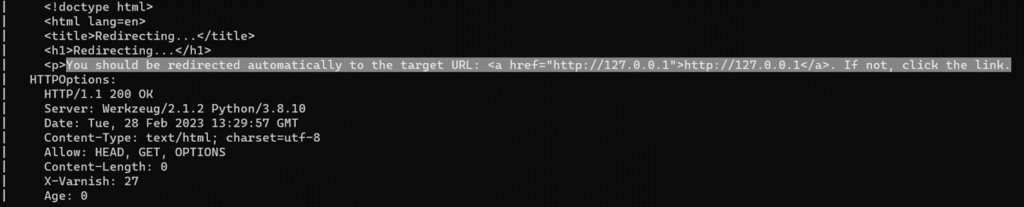
Burpsuite modification

Wait around 1-2 minutes. at netcat you will receive this. Copy the token url.
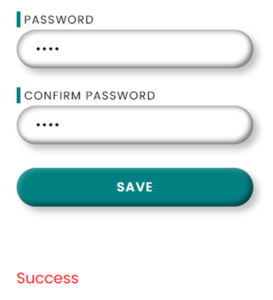
Change password to anything (Here: pass123)

Home Portal



view:source of home, /admin_tickets sounds like an important subdomain

Submit!

Admin cookie, if this fails, repeats by summiting a new ticket with a new folder


And we are in! Look, there is an ssh issue

view:source of /admin_tickets… {diego:dCb#1!x0%gjq}

Get the user.txt


It’s connected to SQL! Nice.

app's Tables

Content of users table

Now [Term] is [Root]

Root flag!